2025NepCTF
NepCTF-MISC-WP
客服小美
1 | 2025年的一个午后,客服小美满怀期待地点开了那封标题为“关于2025年部分节假日安排”的邮件,结果嘛……你懂的,套路来了!作为应急响应界的“技术侦探”,现在轮到你出手啦!你的任务是找出被控机器的用户名、揪出那个偷偷通信的钓鱼木马地址,顺便看看有没有啥敏感信息被顺走。快来动动脑,展现你破案如神的本领吧!flag格式例如:NepCTF{xiaomei_8.8.8.8:11451_secret} |
中规中矩的内存取证+流量分析题
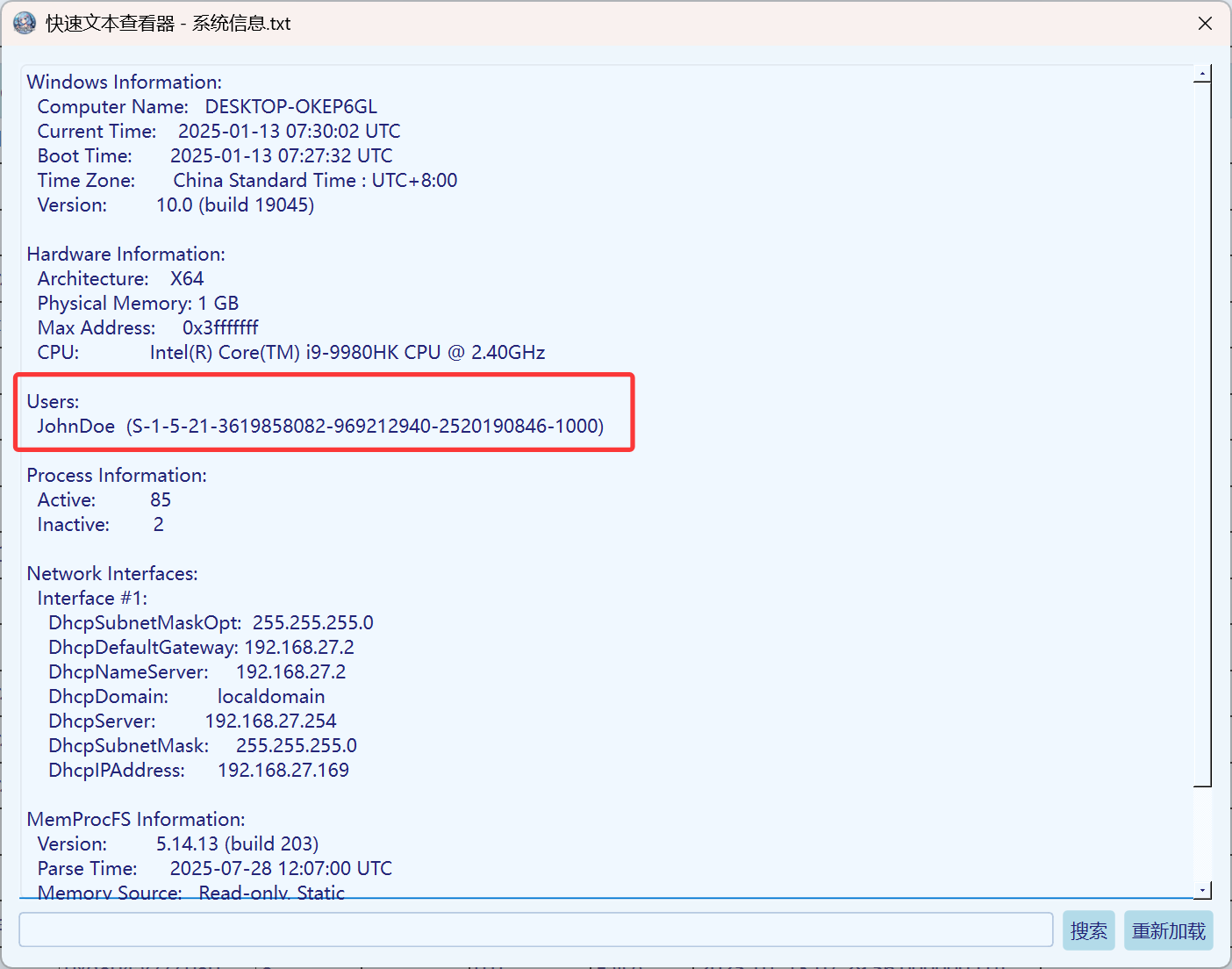
在系统信息中得知被控机器的用户名 JohnDoe
根据题目描述可知,应该是点击了恶意软件导致的,查找网络连接信息,得知钓鱼木马地址为192.168.27.132:12580

这俩很快就能找到,偷走的敏感信息估计在流量中
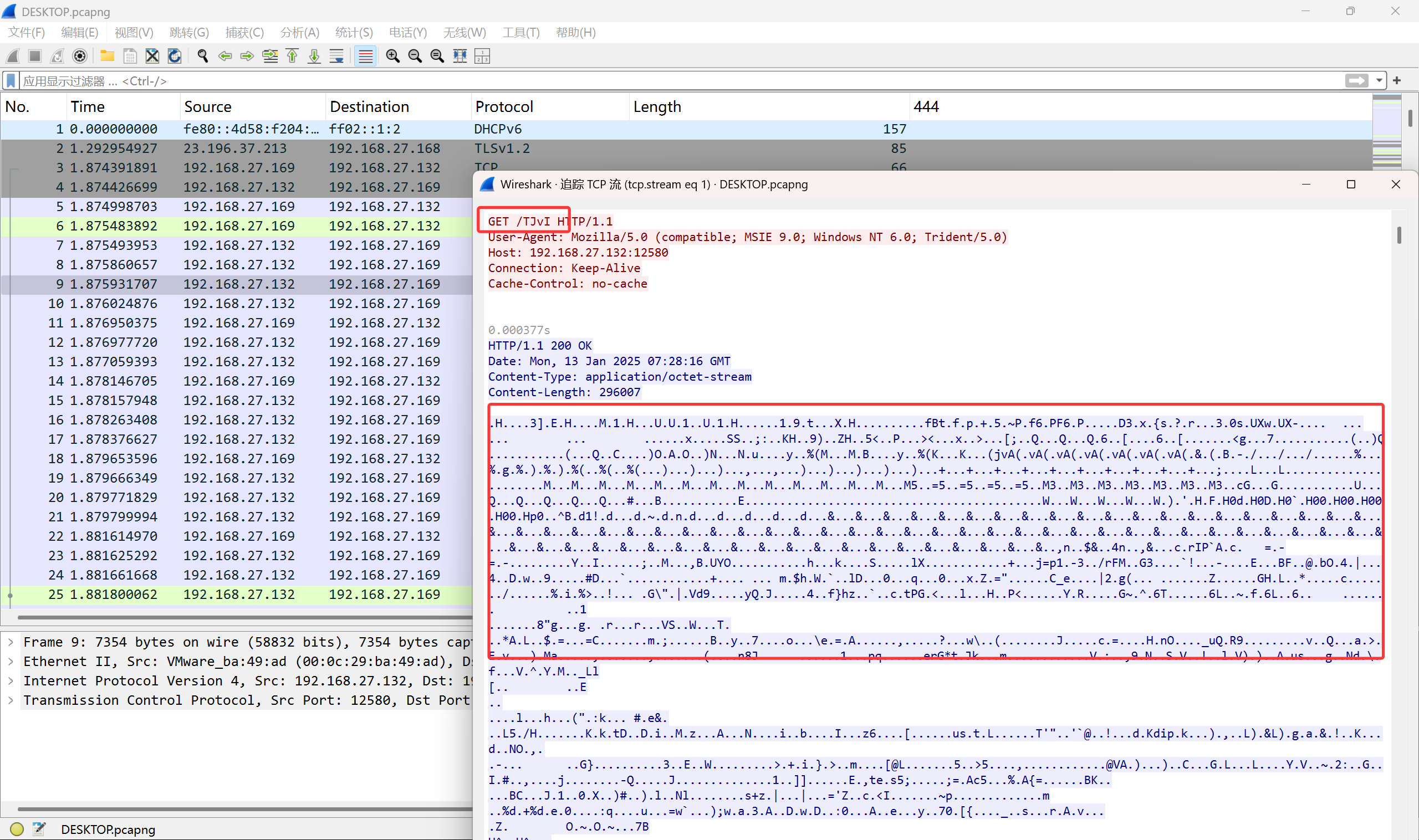
打开流量文件,根据流量特征和GET路由/TJvI判断为Cobalt Strike流量
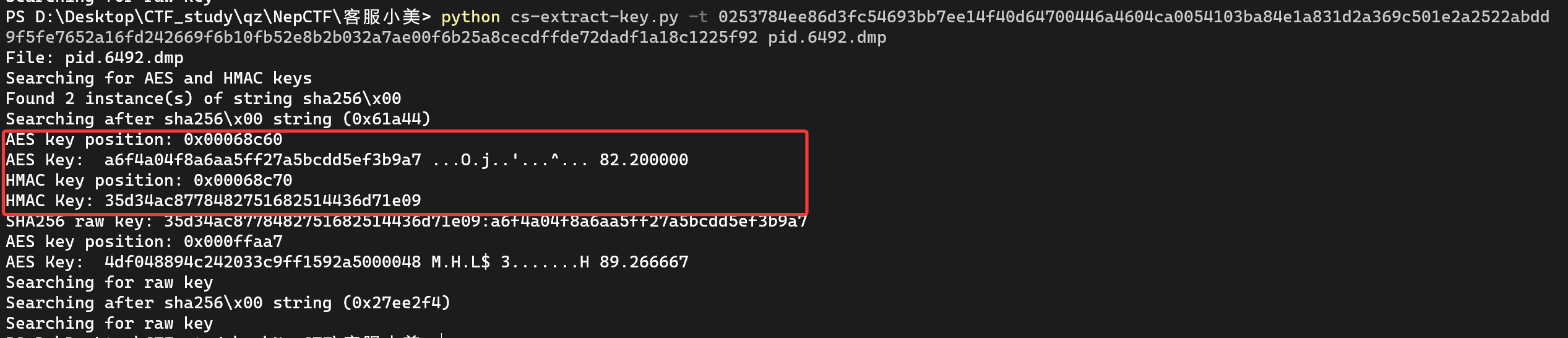
由于找不到.cobaltstrike.beacon_keys文件,无法正常找寻密钥,遂只能从内存中寻找,将进程的内存dump出来(vol3和memprocfs都可,不过在内存的索引上有所区别)使用下边的脚本结合流量内容在dump中寻找AES key和HMAC key
DidierStevensSuite/cs-extract-key.py at master · DidierStevens/DidierStevensSuite
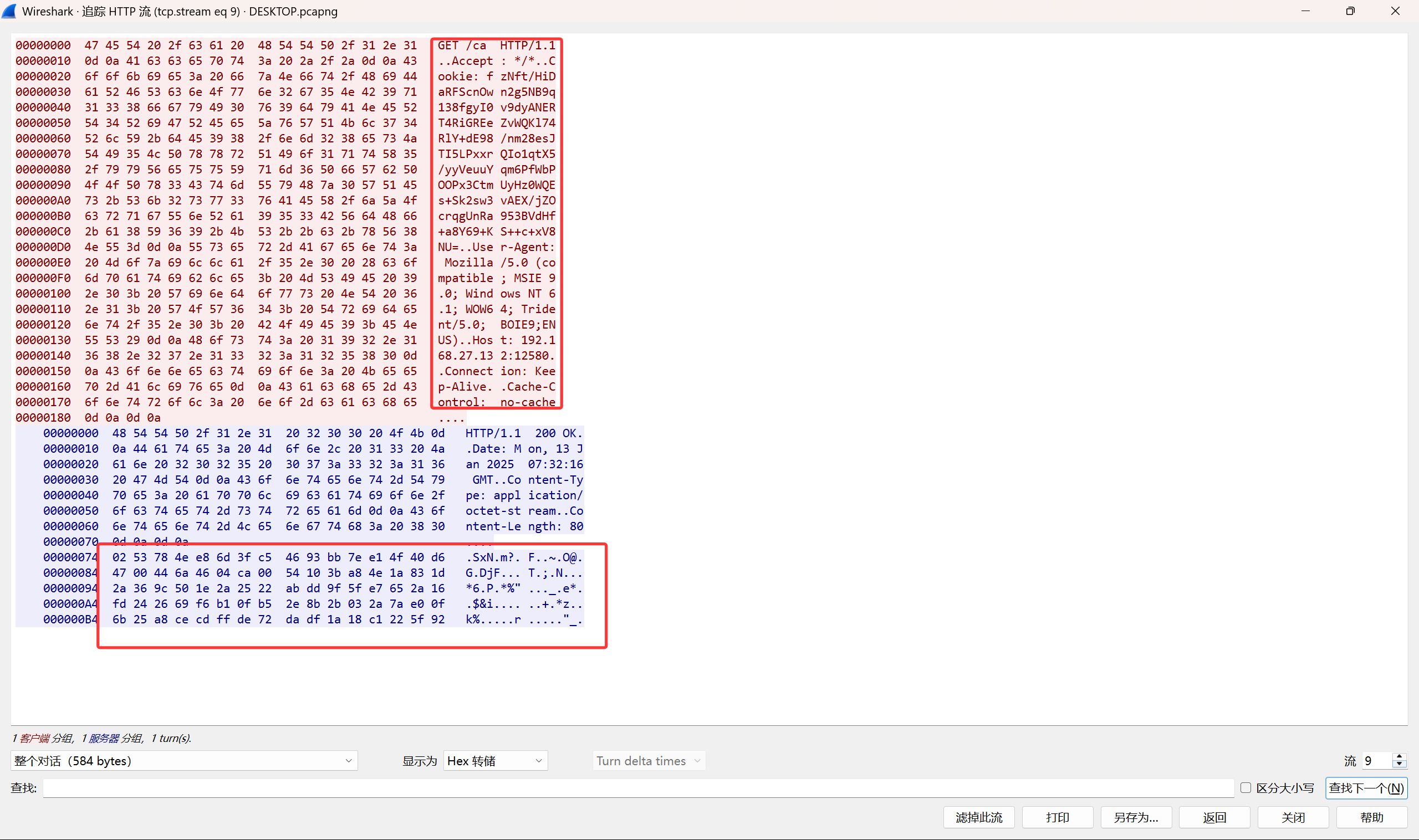
在流量的流9中从钓鱼木马地址接受的指令(其他的流除了接收的任务就是发送的信息,这个需要一个个找一下,比较耗时间)
使用工具破解密钥
1 | python cs-extract-key.py -t 0253784ee86d3fc54693bb7ee14f40d64700446a4604ca0054103ba84e1a831d2a369c501e2a2522abdd9f5fe7652a16fd242669f6b10fb52e8b2b032a7ae00f6b25a8cecdffde72dadf1a18c1225f92 pid.6492.dmp |
vol3dump出的:
memprocfs dump出的:
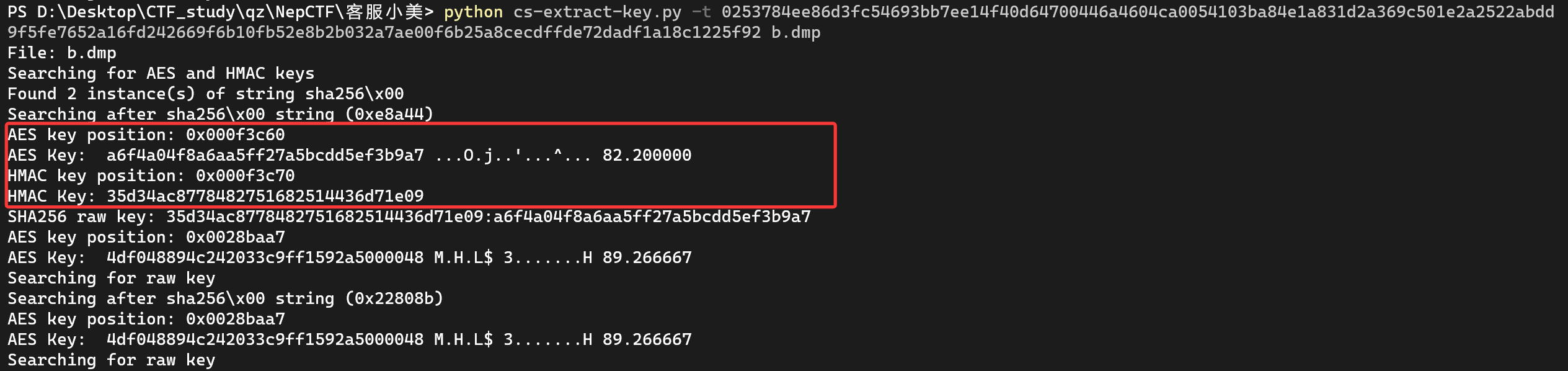
内容一样,positions不一样罢了
同样将其对应的响应也跑一下
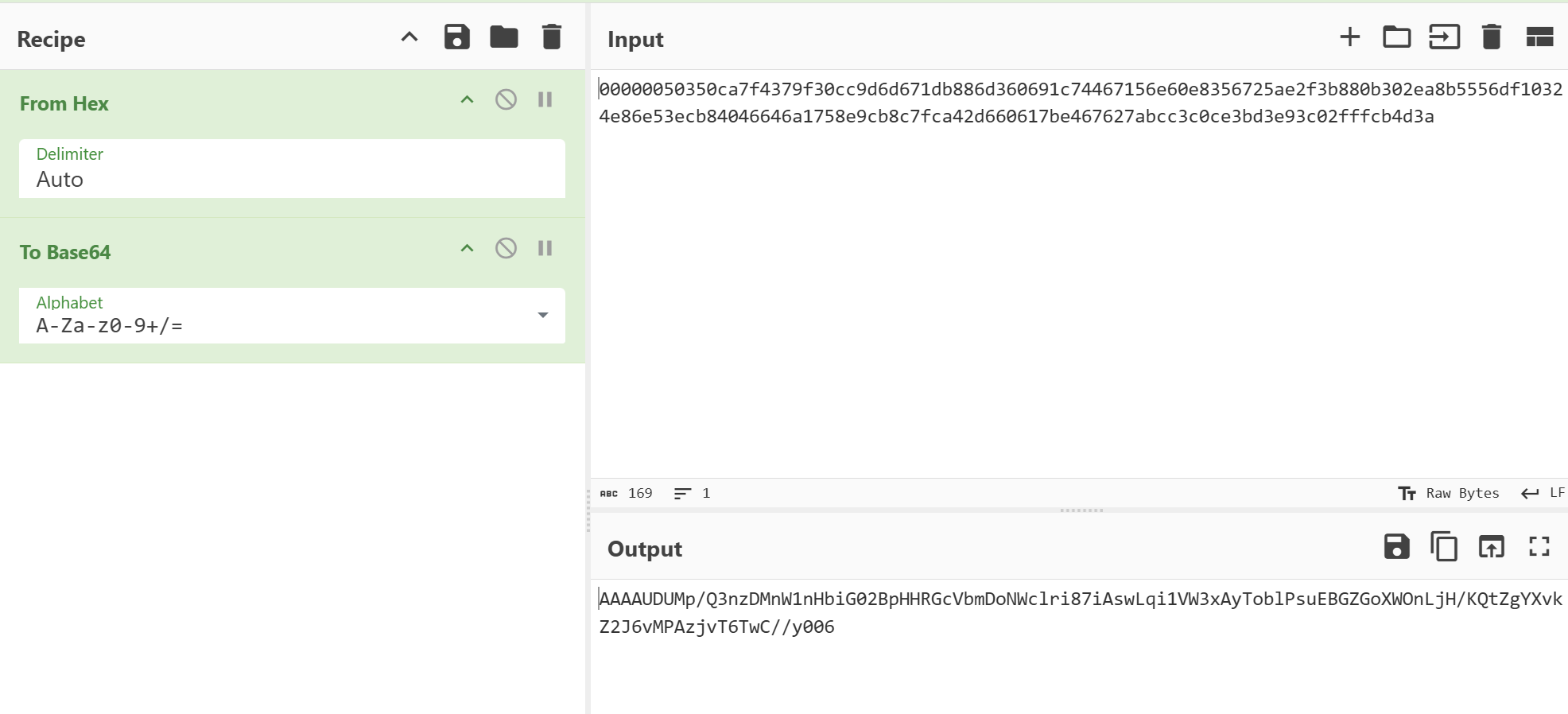
1 | python cs-extract-key.py -c 00000050350ca7f4379f30cc9d6d671db886d360691c74467156e60e8356725ae2f3b880b302ea8b5556df10324e86e53ecb84046646a1758e9cb8c7fca42d660617be467627abcc3c0ce3bd3e93c02fffcb4d3a pid.6492.dmp |
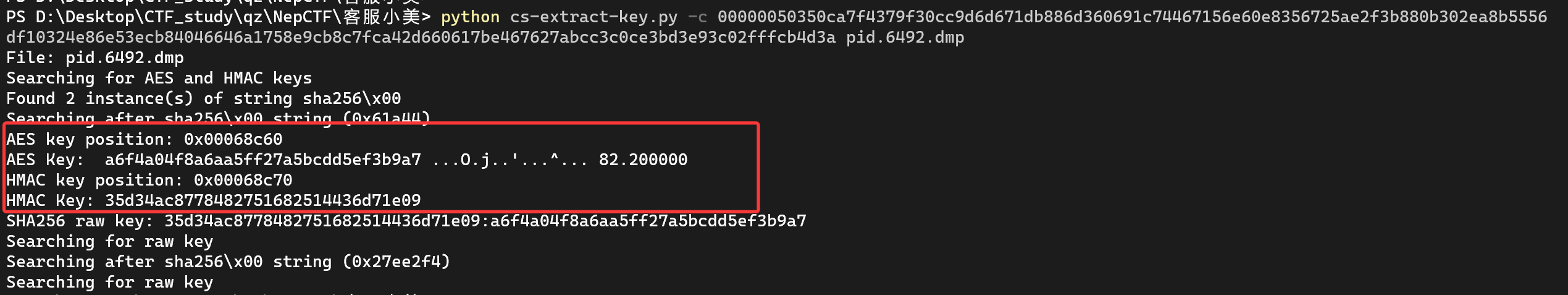
可确定密钥
1 | AES Key: a6f4a04f8a6aa5ff27a5bcdd5ef3b9a7 |
再使用这个项目下的脚本进行解密CS_Decrypt/CS_Task_AES_Decrypt.py at main · WBGlIl/CS_Decrypt
把接受的指令转成base64
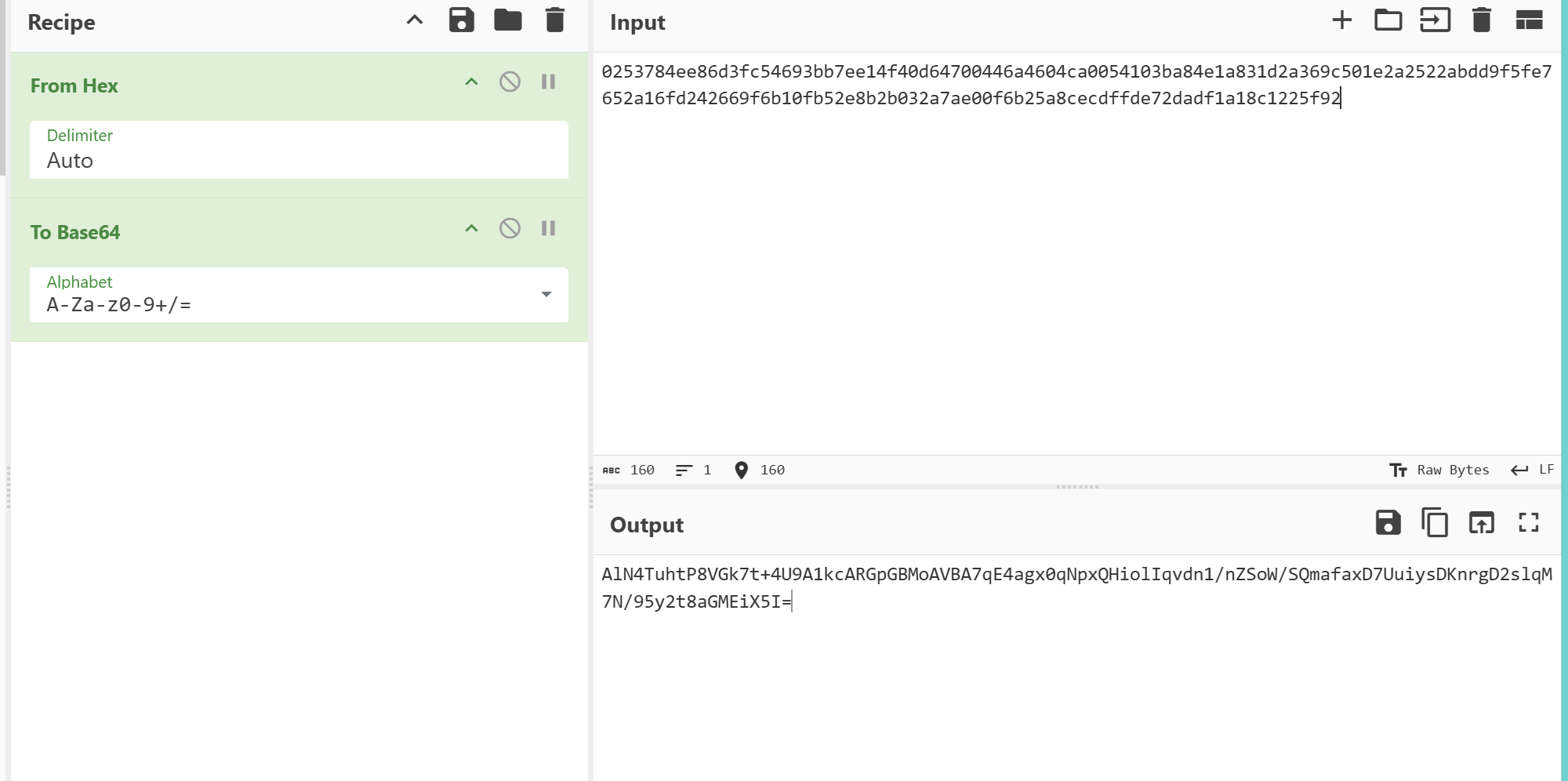
1 | ''' |
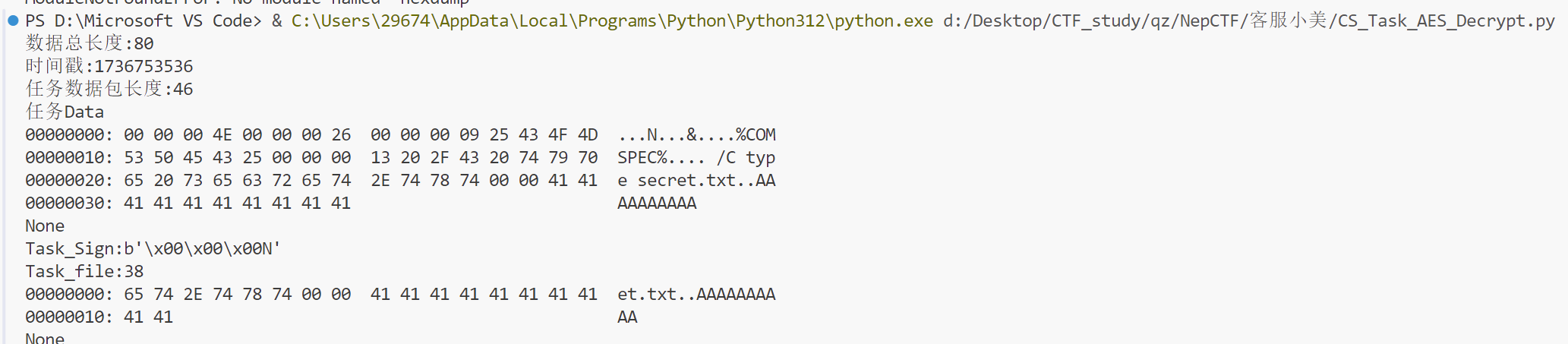
%COMPSPEC%- 作用:Windows系统环境变量,通常解析为
C:\Windows\System32\cmd.exe - 攻击意图:确保在任何Windows系统上都能定位到命令行解释器(绕过路径限制)
- 作用:Windows系统环境变量,通常解析为
/C:执行命令后关闭cmd进程(隐蔽性)type secret.txt:读取secret.txt文件内容并输出到终端- 读取敏感文件
secret.txt,C2服务器通过Beacon接收命令输出(文件内容)
同样把发送的秘密也转成base64
然后用同一项目下的返回解密脚本解密返回内容CS_Decrypt/Beacon_Task_return_AES_Decrypt.py at main · WBGlIl/CS_Decrypt
1 | # -*- coding: utf-8 -*- |
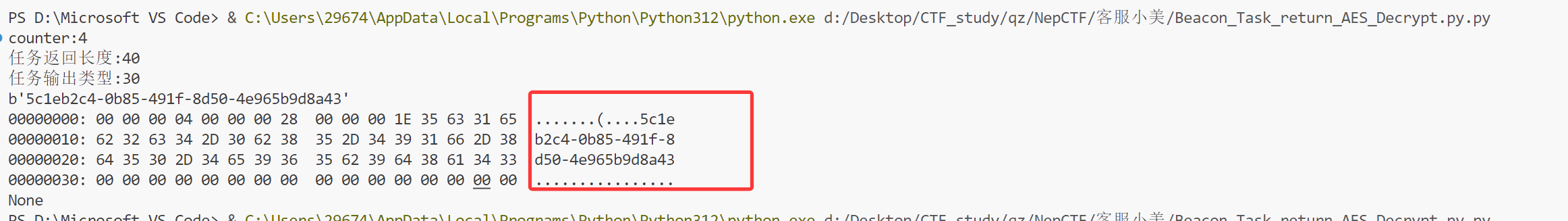
最终得到flag
NepCTF{JohnDoe_192.168.27.132:12580_5c1eb2c4-0b85-491f-8d50-4e965b9d8a43}
NepBotEvent
1 | 最近总觉得NepBot不对劲,邀请函生成速度慢也就算了,以至于/home/Nepnep/目录下都被创建了flag.txt,吓得他赶紧拔网线跑路。经过初步排查,Neper在他的机器上发现了一个神秘的键盘记录器(Keylogger)残留痕迹! |
首先打开所给的压缩包时,注意到
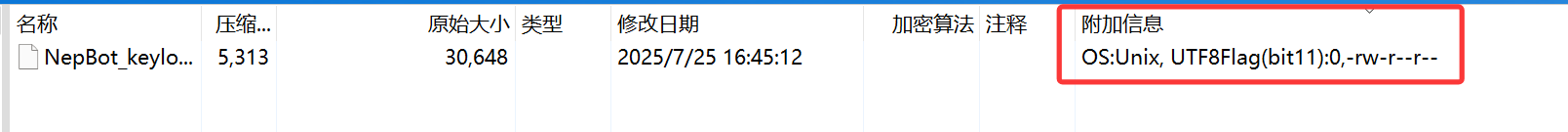
可见该文件的系统是unix
7z打开还可以发现这种东西
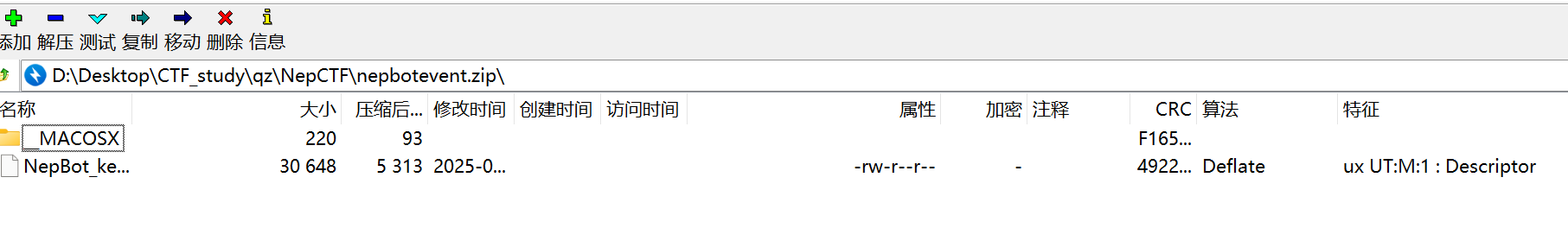
可见确切的说是macos系统的记录键盘的文件,拷打ai给出脚本
1 | import os |
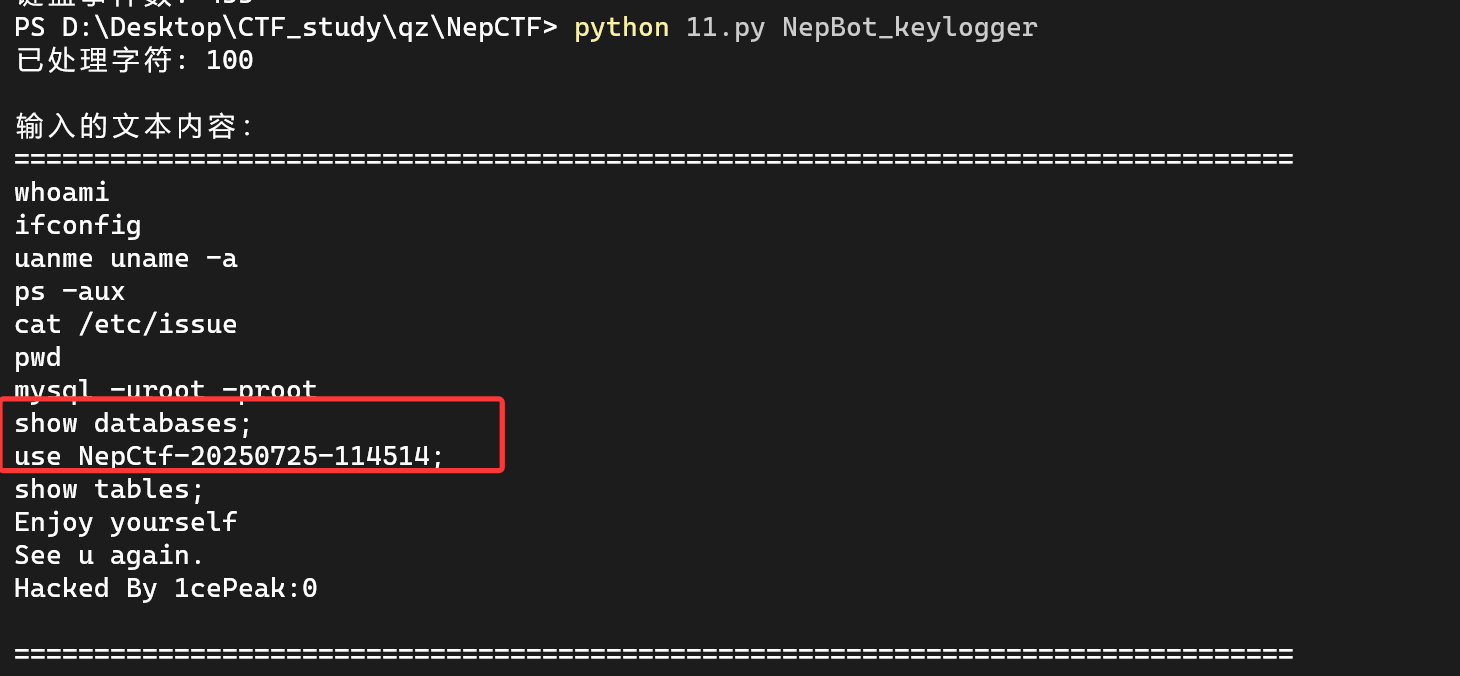
但交上去不对,看一下代码发现有点错误,对与大小写的判定逻辑有错误,遂Ctf应为CTF(毕竟大小写转换只按一次),修改代码后就对了
1 | import os |
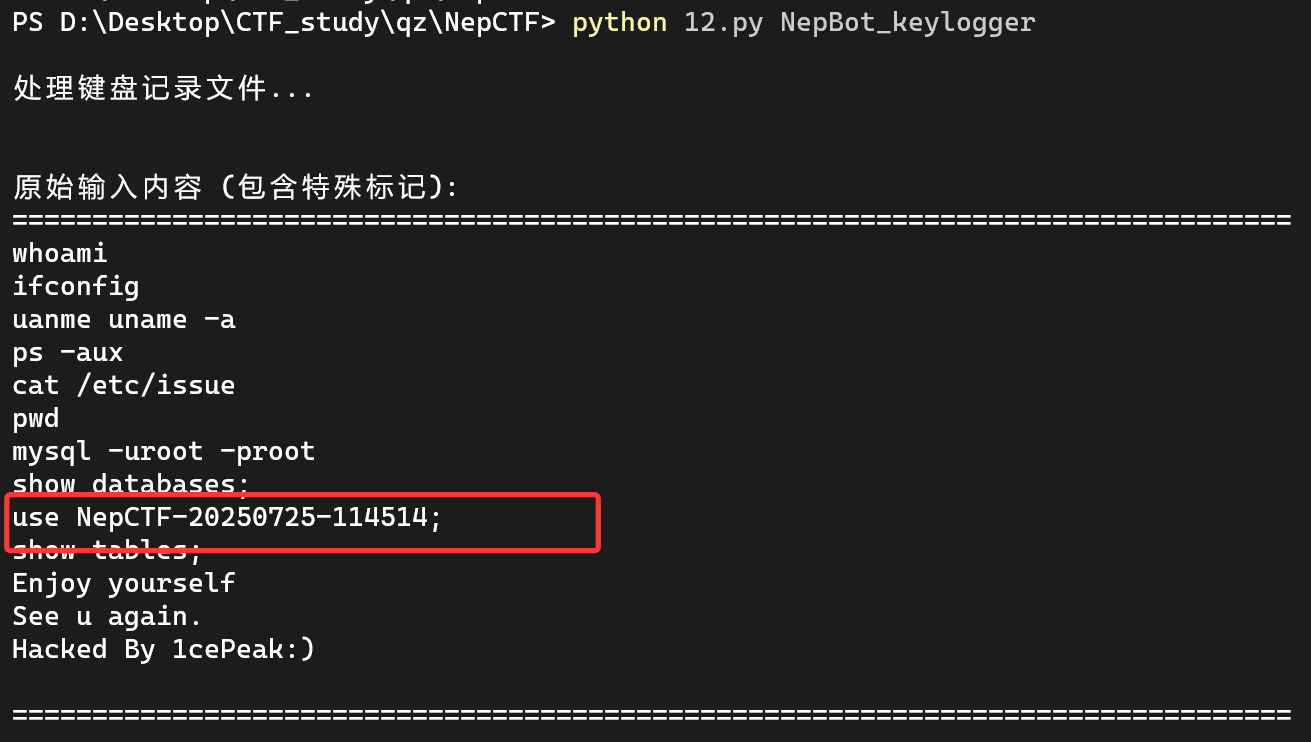
NepCTF{NepCTF-20250725-114514}
SpeedMino
1 | Welcome to SpeedMino! Reach 2600.00 to get FLAG |
经典俄罗斯方块,大概可以用cheat engine破解
游玩时发现北京有一串字符变化,猜测是在解密之类的,遂加快速度,cheat engine
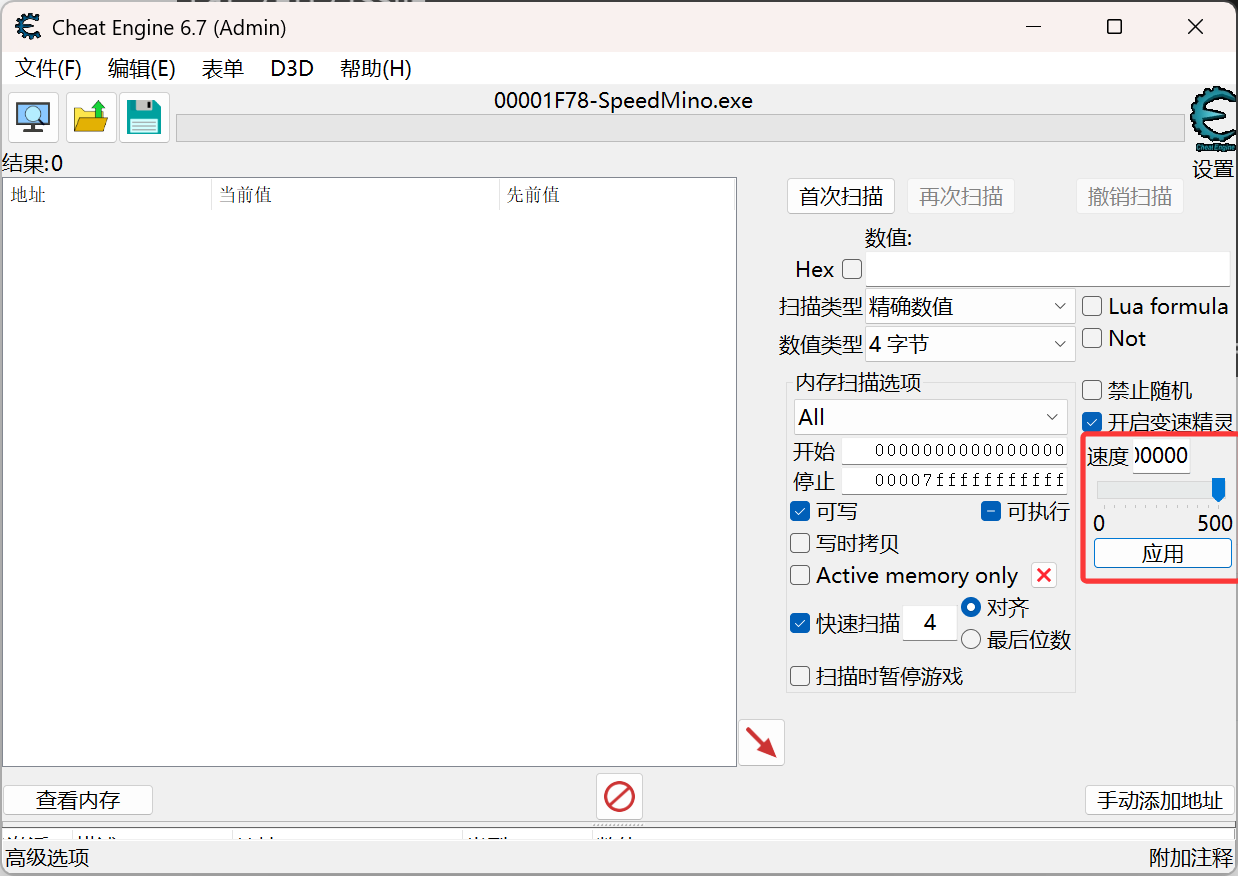
速度改为100000000000000000000000000000,马上出现flag
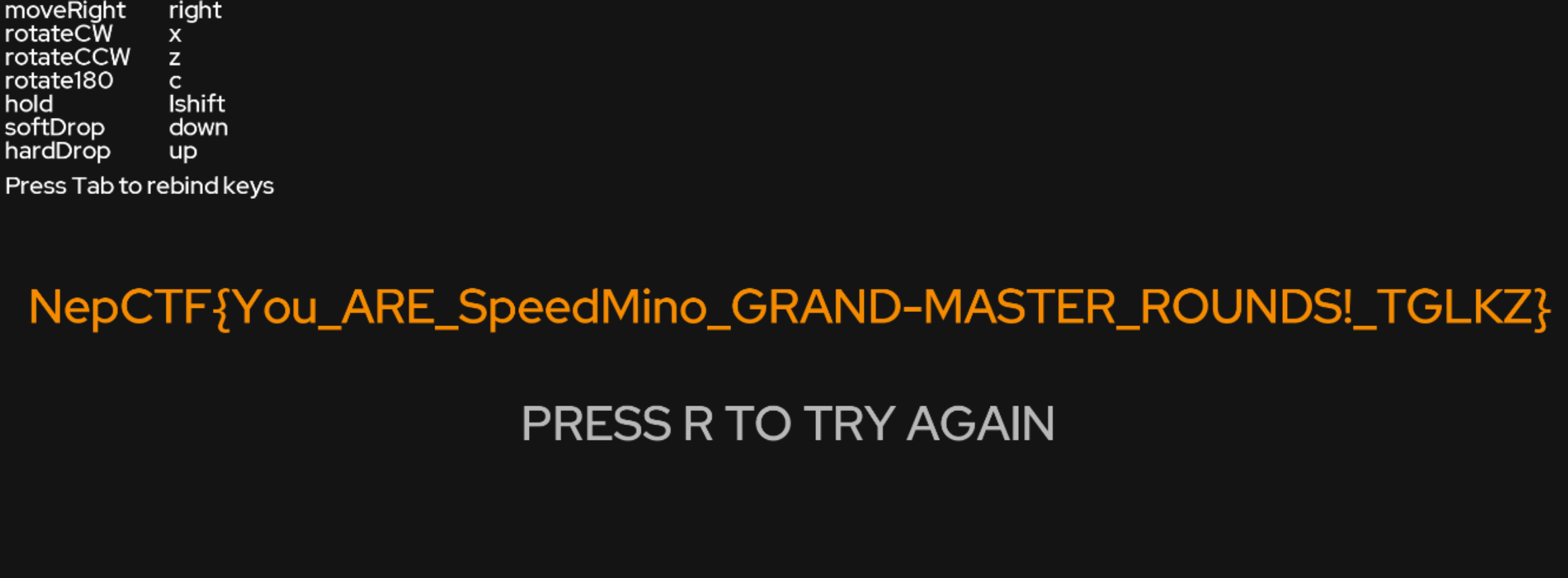
把exe文件解压后发现使用lua写的,根据给的代码也能拷打ai给出解密脚本
Nepsign
拷打gemini2.5 pro得到脚本
1 | from pwn import * |
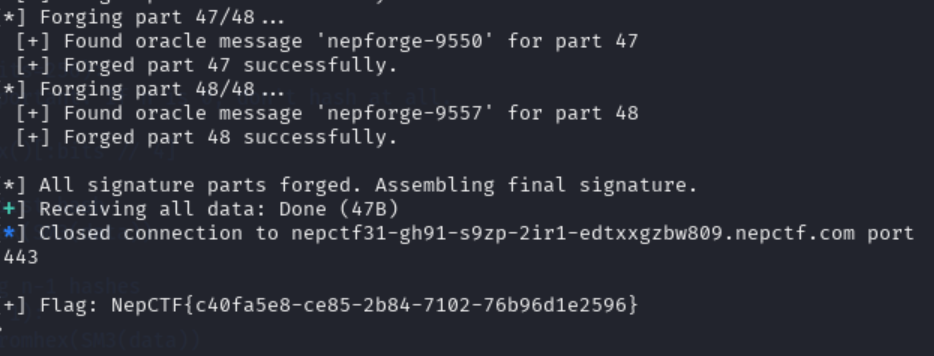
NepCTF{c40fa5e8-ce85-2b84-7102-76b96d1e2596}